The cloud offers firms huge opportunities to expand and scale, yet 96% of them are moderate to extremely concerned about cloud security.
Since its debut, firms have viewed the cloud as a way to push the boundaries of innovation. But cloud security breaches in the cloud have become more regular than on-premises attacks.
As per a recent report by Fortinet, “2024 Cloud Security Report,”

Hence, it is essential to conduct cloud security audits to ensure that cloud apps and data are safe from theft and breaches.
What is a Cloud Security Auditing?
Typically conducted by an independent third party, a cloud security audit tests cloud systems and verifies whether they comply with regulations, industry standards, or security benchmarks.
The audits commonly focus on a firm’s operational, procedural, or technical security controls. The auditor collects evidence via physical inspection, inquiry, observation, or analytics.
Audits also involve checking which security controls exist and whether they are enforced correctly. They must also ensure they are working as expected and are effectively fighting threats.
Why are Cloud Security Audits Required?
APIs and Third Party Tools
Cloud uses diverse APIs and third-party tools, each of which is a potential security risk. Audits can help identify security gaps in APIs and tools and help firms remediate them quickly.
Backup Strategies
Backing up data is easy with the cloud. However, the cloud must be configured properly to carry out the backups. An audit can ensure the firm performs backups for all critical systems and adopts security measures to secure those backups.
Access Control and Secure Access
Employees join and leave the firms or move to new roles or departments. A security audit ensures secure management of access controls. The audits can also help verify that employees and other users access cloud systems securely.
What are the Key Considerations to Keep in Mind During Cloud Security Audit?
Cloud Provider’s Security Posture
The first step of a cloud security audit is testing the provider’s security posture and acquiring vital details. As part of the audit, security procedures and policies are checked, and the risks inherent in cloud systems are determined based on reliable data from the systems.
Understand their shared responsibility model—what they are responsible for and what has to be managed.
Know the provider’s capabilities and ensure they align with business continuity and disaster recovery (DR) plans. Evaluate the strength of backup and restore procedures.
Even if the recovery plan involves support for multiple regions or even multiple clouds, firms and auditors can plot the details to ensure the reliability of the service and uninterrupted operations.
Also Read: Essential Cloud Security Best Practices
Attack Surface
Cloud settings are intricate and have minimal visibility. Firms must use advanced monitoring and observability tools to identify the attack surface. This will help prioritize assets at higher risk and dedicate remediation efforts.
Understand what apps are running within cloud instances and containers. Know whether they are approved or represent shadow IT. Moreover, all workloads must be standardized, and security measures must be checked to ensure compliance. This type of monitoring can address the challenges of the shared responsibility model.
Strong Access Controls
Access management breaches are one of the major cloud security risks. There are many ways hackers can access credentials to critical cloud resources.
As per a report by Orca Security, “2024 State of Cloud Security Report,”
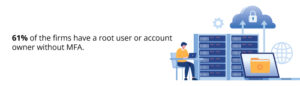
Firms can minimize the risks by
- Creating strong password standards and policies
- Making MFA a must
- Restricting administrative privileges
- Practicing the least privilege principle
External Sharing Standards
Firms must implement standards for data sharing via shared drives, calendars, files, and folders. Begin with the strictest standards. Folders and files featuring the most sensitive data, like PII, financial, and protected medical information (PHI), should not be permitted for external access and sharing. Minimize security restrictions when needed.
Automated Patching
Patching regularly is essential for a secure cloud environment. The key to effective patching is to focus on the most important assets. Ensure that these assets are patched automatically and regularly. Complement automation with regular manual reviews to see if the patching mechanisms are functioning properly.
SIEM for Cloud Logs Standardization
Security information and event management (SIEM) systems help comply with industry standards and regulations. Log management, a function of SIEM, audits activity on an IT network that helps collect cloud logs in a standardized format. They allow auditors to automatically check the data and generate reports for various compliance standards.
Older Vulnerabilities
Vulnerabilities in cloud environments might have existed even before the advent of cloud computing.
Orca Security’s report also states that-
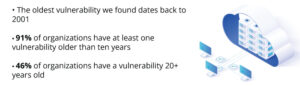
As firms move applications from on-premises setup to the cloud—a process called ‘lift and shift’—existing vulnerabilities are often moved with them.
This means vulnerabilities originally found in the local server become a part of the cloud unless addressed explicitly during the migration process. Cloud security audits help ensure that old liabilities cannot compromise new cloud environments.
Conclusion
As the cloud becomes integral to firms’ operations, the importance of robust cloud security auditing cannot be understated. With the rising prevalence of cloud-based security breaches, it’s clear that firms must adopt a proactive posture in protecting their digital assets.
With these cloud security considerations, firms can significantly enhance their defenses against potential threats. Given the complexity and evolving nature of cloud environments, these audits are not just a regulatory compliance exercise but a critical component of a comprehensive security strategy.
By prioritizing these areas, firms can ensure that their move to the cloud amplifies their potential for growth rather than exposing them to undue risk.
For more such updates follow us on Google News ITsecuritywire News. Please subscribe to our Newsletter for more updates.









