Insider threats can be challenging to detect. In most cases, they may go unnoticed for a long time. Companies should have proper insider threat management practices to detect and respond to potential risks.
While most cybersecurity threats come from outside organizations, insider threats are increasing. And they are dangerous!
Zach Fleming, Head of Red Teaming, Integrity360, says, “Ways of working with threat actors are becoming harder to detect, with insider threats pretending to accidentally slip up in providing attackers access to systems and information.”
From the Seven Key Insights from the 2023 Verizon Data Breach Investigations Report,
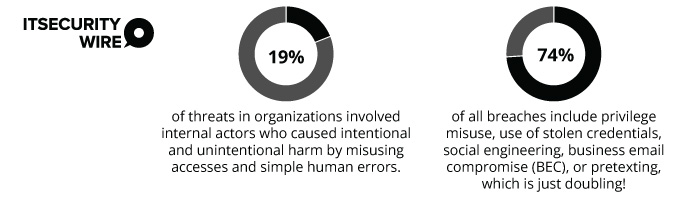
To ensure CISO focus more on the possibilities of such threats, here’s what the report says,
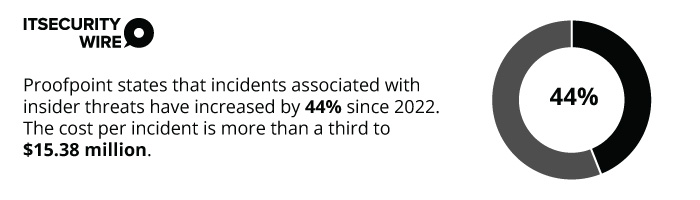
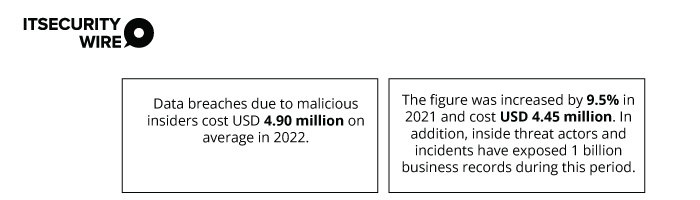
Research report 2022 Ponemon Cost of Insider Threats Global Report,
This article highlights ways to mitigate insider threats by properly implementing best practices.
What are Insider Threats & their Types?
Insider threats usually enter through authorized users, employees, or business partners who intentionally or accidentally misuse their access.
The risk of this penetration is high and could cost the company hefty amounts.
According to IBM’s Cost of a Data Breach Report 2023 report,
Insider threats are categorized as originating from intentional and non-intentional users. But they are broadly defined into two large groups based on their intentions:
- Malicious: These threats are caused intentionally, where threat actors use access to sensitive data to harm the company.
- Inadvertent insiders: They cause damage to the company unintentionally.
Here are some common ones that originate unknowingly under these categories.
1. Negligent insiders
They create security threats due to carelessness or ignorance. Some serious security threats include phishing attacks, security control bypasses, and open passwords.
They also include unauthorized access to organizational networks, wrong email access, and sharing sensitive data with outsiders.
2. Compromised Insiders
These originate among authentic users. Usually, outsiders steal their credentials with malicious intent to access businesses’ secured areas. But companies see them as an insider. Such threats are costly.
From the same Proofpoint Research Report stated above,

Threat actors steal user credentials by:
- Using social engineering strategies, specifically voice phishing in customer support
- Sending phishing emails
- Obtaining customer names and email addresses to phish authentic users in the company itself
- Phishing phone calls
- Infecting a computer with malware through a link in an email, files downloaded from a website, or USB devices
- Pass-the-hash attacks
 Zach Fleming adds,” If you’re that insider threat actor/employee, it’s a high reward and low risk, you can’t go to prison for being bad at spotting a phishing email. And now, for an extra 10% fee, they’ll start washing the money through legitimate shell companies. That’s becoming rampant – some ransomware groups have started doing it, and we’re picking up on it quickly.”
Zach Fleming adds,” If you’re that insider threat actor/employee, it’s a high reward and low risk, you can’t go to prison for being bad at spotting a phishing email. And now, for an extra 10% fee, they’ll start washing the money through legitimate shell companies. That’s becoming rampant – some ransomware groups have started doing it, and we’re picking up on it quickly.”
3. Disgruntled employee
They are attackers who seek to harm organizations as revenge based on their emotional motivations. They usually know a company’s sensitive areas for data storage and are also aware of the overall cyber security system from within.
For such employees, bypassing data or other crucial business assets becomes easy to breach. They often make money on these breaches.
Zach Fleming adds,’ If you’re a disgruntled employee and you work in a company as a helpdesk engineer, they’ll send you an email where you’ll deliberately click on a link where you’ll give them credentials to access a company portal. And then, if they’re successful in extorting the company, they’ll pay that employee up to 70% of whatever the extortion amount was.
4. Careless employees
This includes employees or company partners who ignore the rules of an organization’s cybersecurity policies and commit breaches. They are categorized among intentional insider threats with no malicious intent.
The 2023 Insider Threat Report by Cybersecurity Insiders study says
According to this report, the top three insider threats came from:
- Regular employees
- Privileged users
- Third parties
An instance of a regular employee insider attack was discovered when Yahoo was under this attack in May 2022. One of its senior research scientists stole confidential information about Yahoo’s AdLearn product. The stolen data included 570,000 files that contained backend architecture information, source code, secret algorithms, and other crucial information.
Some crucial risks like fraud, data theft, and system sabotage were the talk of the town to these attacks.
Companies should implement best practices for insider threats to manage and overcome the risks.
Also Read: Strategies to Identify and Mitigate Insider Threats
Best Practices for Insider Threat Management
1. Turning employees into advocates
Employees can also be a part of risk programs under insider threat to report unsafe behavior across data usages, serves, application usages, and more.
As a case in point, Apple employees spotted secret theft and were found guilty of taking images of a secret workplace after Apple conducted some research. The theft contained over two thousand files containing confidential and copyrighted Apple material.
Another example is when employees of manufacturer Cree founded an SD card with 32,000 files, which contained trade secrets worth $100 million.
How do companies turn employees into security advocates for the brand?
- Companies can train employees about its impact by providing security detection training on lost IP or customer data and retrieving it when required.
- Companies should make the insider risk management (IRM) program open instead of a secret. Many of the latest IRM programs include employee training and communication sessions as mandatory in companies.
- Provide employees with password management platforms to ensure strong passwords are used across the business. Installation of antivirus software on all devices remains mandatory.
- Employees should be trained to use data loss prevention (DLP) tools to track and prevent data breaches. However, DLP solutions should integrate seamlessly with existing infrastructure and actively manage policies to keep insider threats away.
2. Recognize Malicious insiders
Employees should have tools to recognize malicious insider threats. Security teams can install threat detection tools into systems that constantly notice changes in usages, access, functions, and operations to look for signals of possible threats.
AI and automation tools can help by:
- Installing user activity monitoring tools to detect fraudulent activities like using sensitive data and restricted access information.
- Install access management tools that restrict access to sensitive data to avoid sabotage in organizational systems or data.
- Install user and behavior analytics to see if any suspicious activities are happening. Activities such as data theft or information breaches can be identified on behalf of other parties.
To stop malicious insiders, IT security teams should install tools to protect emails from malware and hackers. Tools like Secure Email Gateways, anti-malware software, and anti-phishing tools like the Cofense suite of products are available.
These tools detect and block emails containing malware, malicious URLs, or suspicious attachments.
This step is necessary because threats sent through an internal email can be intercepted at a secure email gateway.
3. Employ threat modeling
This can be done in various ways:
- Adopt threat modeling to determine the threat,
- allow appropriate security controls to identify threats, their objectives, and vulnerabilities and
- understand potential attack vectors.
Threat modeling should be an essential part of software design and development.
Security teams need to decide what the model will cover to implement it correctly. For instance, is it focused on a particular application, a network, or the application and the infrastructure it runs on?
Based on this, they can classify each data. This way, the team can determine threats and vulnerabilities while simultaneously automating the mitigation processes.
Some threat modeling methodologies, like process flow diagrams, are commonly used today. It shows an application or system from the user’s point of interaction and how attackers monitor their actions and move throughout the application. This process flow makes it easier to spot and prioritize potential insider threats.
Similarly, companies can use the Attack trees methodology to visualize attacks on a system or to evaluate a specific type of insider attack on applications and systems.
Also Read: Pitfalls of Ignoring Insider Threats in IT Security
4. Controlling access to systems and data
To reduce threats inside businesses, security teams must minimize or control access to systems and data by employees, business partners, or third parties.
Companies should implement a zero-trust architecture (ZTA) to power control measures. This will include approvals and permissions to access or need-based user identity verification before granting access to a critical asset.
Organizations can establish a ZTA in several ways:
- By focusing on user access privilege and context-based identity verification
- By splitting networks into different segments and protecting them with different access coding
- By using software-based perimeter approaches
Implementing Zero trust architecture will increase visibility in all access portals, improve dashboard monitoring, and reduce attack surfaces through monitoring tools.
Conclusion
Employees, business partners, and third parties are essential to the company but also create vulnerability to cyber-attacks.
Their intentional or non-intentional actions can significantly impact an organization’s security framework.
So, CIOs should invest in advanced security technology and empower teams to participate, prepare, and respond to insider threats.
For more such updates follow us on Google News ITsecuritywire News. Please subscribe to our Newsletter for more updates.









