- Most businesses have embraced a radical shift- moving their data from on-premises to the cloud.
- As 2023 ends, many are still struggling with cloud security threats.
Today, most enterprise application deployments, business models, operations, and other essential functionalities reside in the cloud. Hence, in 2024, the rising threats and ways to mitigate them are necessary areas of focus.
Cloud storage has made it feasible for every enterprise to transform into a digital entity.
Unfortunately, cloud advancements have garnered the attention of hackers. There will be a chance of data breaches, ransomware, and malware attacks. Therefore, CISOs and IT leaders must work together to mitigate cloud security threats and stay aware of the latest cloud security threats.
Top cloud security threats in 2024 and the proven mitigation strategies
Malware Attacks
Malware attacks are the most potent cloud threat firms encounter. These attacks often take severe forms, such as Trojans and ransomware, which can help hackers steal sensitive data, disrupt business operations, and even hold data hostage.
With the rising number of malware attacks, firms must maintain an efficient cloud strategy plan in 2024.
Solution:
To mitigate the malware attack risks, firms must-
- Update necessary systems with the latest security patches. Regular updates will help close any vulnerabilities that could be exploited by malware.
- Regularly back up data in the cloud and maintain an offline repository. This will help restore data without additional expenditure in cases of attacks.
- Use network segmentation to limit the spread of malware in the cloud. This way, it becomes easy to limit the damage.
- Use anti-malware software to detect malware in servers and systems and remove it immediately.
- Employ multiple security best practiceslike firewalls, intrusion detection and prevention systems, and antivirus software.
- Implement cloud security methods such as vulnerability scanning, identity and access management, data encryption, and API security.
But, since data is quite tricky to handle and set under control in the cloud, there is an environment of endless data sprawl. Therefore, monitoring cloud systems continuously is essential to avoid malware attacks.
ATO Attacks
Account takeovers (ATO) enable attackers to gain unauthorized access to a user’s account by obtaining login credentials from cloud networks and systems. ATO damages can be immediate and long-lasting- depending on how long the business or account holder takes to notice.
ATO attacks can significantly impact businesses’ financial status by primarily threatening key accounts with confidential data. In 2024, attacks like these will grow and evolve along the cloud infrastructure.
Solution:
To mitigate ATO attacks, firms must-
- Enable multi-factor authorization (MFA) to strengthen your account takeover protection by asking users to provide another method for authentication besides their password.
 Configure Web Application Firewalls (WAFs) to help and block account takeover attacks via targeted policies. These firewalls may help identify signs of brute force attacks and other bad bot activities.
Configure Web Application Firewalls (WAFs) to help and block account takeover attacks via targeted policies. These firewalls may help identify signs of brute force attacks and other bad bot activities.- Deploy a tracking system to track all activities related to the compromised account and block it if necessary.
- Use AI-based ATO detection and protection software to identify and stop sophisticated bot attacks in real-time.
- Hackers use advanced (4th-gen) bots that mimic human behavior, making it challenging for traditional security systems to detect them. Therefore, using advanced AI and ML-based tech for behavior-based detection will help identify complex ATO attempts.
Misconfigurations of Cloud Services
Misconfigurations in a cloud environment can give attackers unauthorized access to system functionality and sensitive data. For example, database server misconfigurations could make data accessible via a basic web search, resulting in a significant data breach.
Cloud misconfigurations can lead to compromise of system security and other severe consequences. This leaves the cloud environment vulnerable to attacks that could cost the firms millions of dollars.
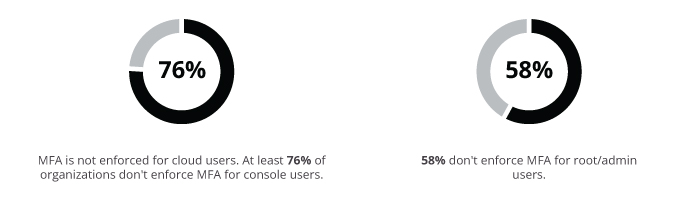
Palo Alto Networks’ report also states that-
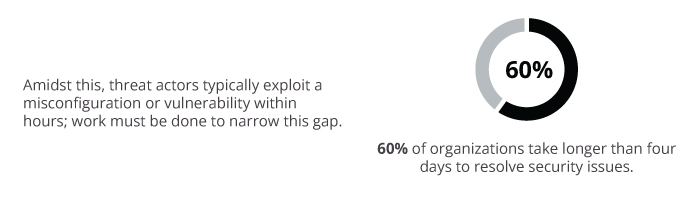
Solution:
To prevent misconfigurations of cloud services, firms must-
- Implement cloud security best practices using industry-standard frameworks such as CIS or NIST.
- Use advanced cloud security tools for automatic detection and fixing misconfigurations.
- Uplift virtual private clouds (VPCs) and network segmentation to create security walls in the cloud.
- Set processes for testing the vulnerabilities to prevent them from entering the cloud infrastructure.
Cloud service misconfigurations are concerns that lead to data breaches, unauthorized access, or other cloud security threats. In 2024, firms must proactively identify and address cloud service misconfigurations and maintain a secure and submissive cloud environment.
Data Breach
 Data breaches occurs due to weak credentials or highly complex accessibility systems. Inadequate cloud configurations or zero protection runtimes leave data vulnerable to theft. In 2024, data breaches will pose the most frequent and severe risk to businesses in the cloud.
Data breaches occurs due to weak credentials or highly complex accessibility systems. Inadequate cloud configurations or zero protection runtimes leave data vulnerable to theft. In 2024, data breaches will pose the most frequent and severe risk to businesses in the cloud.
Thales also stated that-
- Only 22% of firms report that 60% or more of their cloud data is encrypted.
- On average, only 45% of sensitive data is encrypted.
- Only 41% have zero-trust controls on cloud infrastructure, and even fewer (38%) use zero-trust controls in cloud networks.
Solution:
To prevent data breaches, firms must-
- Enable encryption at the cloud network’s edge to safeguard the sensitive data.
- Regularly assess the efficacy of existing encryption protocols to strengthen the security walls.
- Streamline the permission requesting process to ensure all requests to access the data or apps are followed correctly.
- Ensure the safety of all the data stored in the cloud and the apps integrated into the cloud service by keeping a log of all the unusual activities.
- Track the user activities and analyze them for suspicious behavior. This will prevent an outsider from breaching the security and stealing data from the network.
Stay Aware of Cloud Threats Every Time!
In 2024, CISOs must prioritize strengthening their cloud security efforts by understanding the significance and worth of each security wall. By deploying robust theft solutions, firms can move and use the cloud confidently.
For more such updates follow us on Google News ITsecuritywire News. Please subscribe to our Newsletter for more updates.









